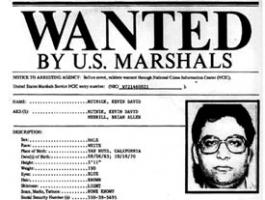
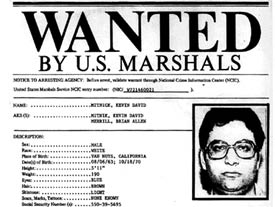
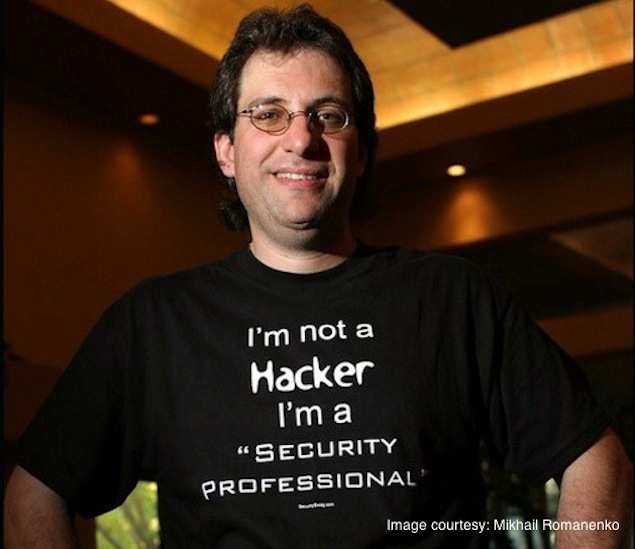
Kevin Mitnick's Profile
Brief about Kevin Mitnick: By info that we know Kevin Mitnick was born at 1963-08-06. And also Kevin Mitnick is American Businessman.
Some Kevin Mitnick's quotes. Goto "Kevin Mitnick's quotation" section for more.I characterize myself as a retired hacker. I'm applying what I know to improve security at companies.
Tags: Hacker, Improve, SecurityI did get a huge endorphin rush when I was able to crack a system because it was like a video game.
Tags: Able, Game, SystemI saw myself as an electronic joy rider.
Tags: Electronic, Joy, RiderI was an accomplished computer trespasser. I don't consider myself a thief.
Tags: Computer, Consider, ThiefI was fascinated with the phone system and how it worked; I became a hacker to get better control over the phone company.
Tags: Company, Control, SystemI was pretty much the government's poster boy for what I had done.
Tags: Done, Government, PrettyOf course I'm sure half the people there hate me and half the people like me.
Tags: Half, Hate, SureSo the ethic I was taught in school resulted in the path I chose in my life following school.
Tags: Life, Path, SchoolSteve Wozniak and Steve Jobs founded Apple Inc, which set the computing world on its ear with the Macintosh in 1984.
Tags: Apple, Computers, JobsThe key to social engineering is influencing a person to do something that allows the hacker to gain access to information or your network.
Tags: Hacker, Key, SocialThe myth of Kevin Mitnick is much more interesting than the reality of Kevin Mitnick. If they told the reality, no one would care.
Tags: Care, Myth, RealityWe have problems with our physical security, operational security through to management.
Tags: Physical, Problems, SecurityBut a lot of businesses out there don't see the return on investment, they look at it as a liability, and until they can understand that proactive security actually returns, gives them a return on investment, it's still a hard sell for people.
Tags: Hard, Understand, UntilI believe in having each device secured and monitoring each device, rather than just monitoring holistically on the network, and then responding in short enough time for damage control.
Tags: Control, Enough, TimeI think malware is a significant threat because the mitigation, like antivirus software, hasn't evolved to a point to really mitigate the risk to a reasonable degree.
Tags: Degree, Point, RiskI was addicted to hacking, more for the intellectual challenge, the curiosity, the seduction of adventure; not for stealing, or causing damage or writing computer viruses.
Tags: Adventure, Challenge, WritingNew security loopholes are constantly popping up because of wireless networking. The cat-and-mouse game between hackers and system administrators is still in full swing.
Tags: Between, Game, SecurityWhen an attacker fails with one person, they often go to another person. The key is to report the attack to other departments. Workers should know to act like they are going along with what the hacker wants and take copious notes so the company will know what the hacker is trying to find.
Tags: Another, Often, TryingRelated topics
- Rhona Mitra
- Dimitri Mitropoulos
- Lakshmi Mittal
- RJ Mitte
- Francois Mitterrand
- David Mixner
- Issey Miyake
- Shigeru Miyamoto
- Hayao Miyazaki
- Kenji Miyazawa