Kevin Mitnick's Quotes
Born: 1963-08-06
Profession: Businessman
Nation: American
Biography of Kevin Mitnick
I characterize myself as a retired hacker. I'm applying what I know to improve security at companies.
Tags: Hacker, Improve, SecurityI did get a huge endorphin rush when I was able to crack a system because it was like a video game.
Tags: Able, Game, SystemI saw myself as an electronic joy rider.
Tags: Electronic, Joy, RiderI was an accomplished computer trespasser. I don't consider myself a thief.
Tags: Computer, Consider, ThiefI was fascinated with the phone system and how it worked; I became a hacker to get better control over the phone company.
Tags: Company, Control, SystemI was pretty much the government's poster boy for what I had done.
Tags: Done, Government, PrettyOf course I'm sure half the people there hate me and half the people like me.
Tags: Half, Hate, SureSo the ethic I was taught in school resulted in the path I chose in my life following school.
Tags: Life, Path, SchoolSteve Wozniak and Steve Jobs founded Apple Inc, which set the computing world on its ear with the Macintosh in 1984.
Tags: Apple, Computers, JobsThe key to social engineering is influencing a person to do something that allows the hacker to gain access to information or your network.
Tags: Hacker, Key, SocialThe myth of Kevin Mitnick is much more interesting than the reality of Kevin Mitnick. If they told the reality, no one would care.
Tags: Care, Myth, RealityWe have problems with our physical security, operational security through to management.
Tags: Physical, Problems, SecurityBut a lot of businesses out there don't see the return on investment, they look at it as a liability, and until they can understand that proactive security actually returns, gives them a return on investment, it's still a hard sell for people.
Tags: Hard, Understand, UntilI believe in having each device secured and monitoring each device, rather than just monitoring holistically on the network, and then responding in short enough time for damage control.
Tags: Control, Enough, TimeI think malware is a significant threat because the mitigation, like antivirus software, hasn't evolved to a point to really mitigate the risk to a reasonable degree.
Tags: Degree, Point, RiskI was addicted to hacking, more for the intellectual challenge, the curiosity, the seduction of adventure; not for stealing, or causing damage or writing computer viruses.
Tags: Adventure, Challenge, WritingNew security loopholes are constantly popping up because of wireless networking. The cat-and-mouse game between hackers and system administrators is still in full swing.
Tags: Between, Game, SecurityWhen an attacker fails with one person, they often go to another person. The key is to report the attack to other departments. Workers should know to act like they are going along with what the hacker wants and take copious notes so the company will know what the hacker is trying to find.
Tags: Another, Often, TryingAny type of operating system that I wanted to be able to hack, I basically compromised the source code, copied it over to the university because I didn't have enough space on my 200 megabyte hard drive.
Tags: Enough, Hard, WantedBoth social engineering and technical attacks played a big part in what I was able to do. It was a hybrid. I used social engineering when it was appropriate, and exploited technical vulnerabilities when it was appropriate.
Tags: Able, Big, UsedComputer hacking really results in financial losses and hassles. The objectives of terrorist groups are more serious. That is not to say that cyber groups can't access a telephone switch in Manhattan on a day like 9/11, shut it down, and therefore cause more casualties.
Tags: Financial, Results, SeriousI can go into LinkedIn and search for network engineers and come up with a list of great spear-phishing targets because they usually have administrator rights over the network. Then I go onto Twitter or Facebook and trick them into doing something, and I have privileged access.
Tags: Engineers, Great, RightsI think it goes back to my high school days. In computer class, the first assignment was to write a program to print the first 100 Fibonacci numbers. Instead, I wrote a program that would steal passwords of students. My teacher gave me an A.
Tags: School, Teacher, WriteI'm an expert witness in a case that's in appeal about a guy who allegedly misappropriated source code from a major, major company - he actually worked there and then apparently they found it on his laptop later.
Tags: Actually, Found, GuyVisit partners pages
Visit partners pages
I'm still a hacker. I get paid for it now. I never received any monetary gain from the hacking I did before. The main difference in what I do now compared to what I did then is that I now do it with authorization.
Tags: Difference, Hacker, PaidIt doesn't work the same way everywhere. The Americans are the most gullible, because they don't like to deny co-workers' requests. People in the former Soviet bloc countries are less trusting, perhaps because of their previous experiences with their countries' secret services.
Tags: Less, Secret, WorkIt's kind of interesting, because hacking is a skill that could be used for criminal purposes or legitimate purposes, and so even though in the past I was hacking for the curiosity, and the thrill, to get a bite of the forbidden fruit of knowledge, I'm now working in the security field as a public speaker.
Tags: Knowledge, Past, WorkingIt's true, I had hacked into a lot of companies, and took copies of the source code to analyze it for security bugs. If I could locate security bugs, I could become better at hacking into their systems. It was all towards becoming a better hacker.
Tags: Become, Security, TrueNo company that I ever hacked into reported any damages, which they were required to do for significant losses. Sun didn't stop using Solaris and DEC didn't stop using VMS.
Tags: Company, Stop, SunNo way, no how did I break into NORAD. That's a complete myth. And I never attempted to access anything considered to be classified government systems.
Tags: Break, Complete, GovernmentSo what I was essentially doing was, I compromised the confidentiality of their proprietary software to advance my agenda of becoming the best at breaking through the lock.
Tags: Becoming, Best, SoftwareSocial engineering is using deception, manipulation and influence to convince a human who has access to a computer system to do something, like click on an attachment in an e-mail.
Tags: Deception, Human, SocialThe perfect PIN is not four digits and not associated with your life, like an old telephone number. It's something easy for you to remember and hard for other people to guess.
Tags: Hard, Life, RememberYou can never protect yourself 100%. What you do is protect yourself as much as possible and mitigate risk to an acceptable degree. You can never remove all risk.
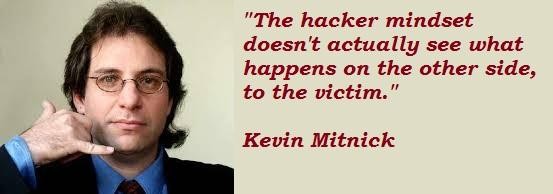
Tags: Possible, Risk, YourselfThe hacker mindset doesn't actually see what happens on the other side, to the victim.
Tags: Actually, Happens, SideMy actions constituted pure hacking that resulted in relatively trivial expenses for the companies involved, despite the government's false claims.
Tags: Actions, Government, InvolvedSocial engineering is using manipulation, influence and deception to get a person, a trusted insider within an organization, to comply with a request, and the request is usually to release information or to perform some sort of action item that benefits that attacker.
Tags: Action, Deception, SocialAll they need to do is to set up some website somewhere selling some bogus product at twenty percent of the normal market prices and people are going to be tricked into providing their credit card numbers.
Tags: Market, Normal, PercentSecurity is always going to be a cat and mouse game because there'll be people out there that are hunting for the zero day award, you have people that don't have configuration management, don't have vulnerability management, don't have patch management.
Tags: Game, Management, SecurityI made stupid decisions as a kid, or as a young adult, but I'm trying to be now, I'm trying to take this lemon and make lemonade.
Tags: Stupid, Trying, YoungI get hired by companies to hack into their systems and break into their physical facilities to find security holes. Our success rate is 100%; we've always found a hole.
Tags: Found, Security, SuccessChoosing a hard-to-guess, but easy-to-remember password is important!
Tags: ChoosingGarbage can provide important details for hackers: names, telephone numbers, a company's internal jargon.
Tags: Company, Hackers, NumbersI could have evaded the FBI a lot longer if I had been able to control my passion for hacking.
Tags: Able, Control, PassionI get hired to hack into computers now and sometimes it's actually easier than it was years ago.
Tags: Actually, Computers, SometimesMy argument is not that I shouldn't have been punished, but that the punishment didn't fit the crime.
Tags: Argument, Crime, FitSome people think technology has the answers.
Tags: Answers, TechnologyA company can spend hundreds of thousands of dollars on firewalls, intrusion detection systems and encryption and other security technologies, but if an attacker can call one trusted person within the company, and that person complies, and if the attacker gets in, then all that money spent on technology is essentially wasted.
Tags: Money, Security, TechnologyAre hackers a threat? The degree of threat presented by any conduct, whether legal or illegal, depends on the actions and intent of the individual and the harm they cause.
Tags: Individual, Legal, WhetherHackers are breaking the systems for profit. Before, it was about intellectual curiosity and pursuit of knowledge and thrill, and now hacking is big business.
Tags: Big, Business, KnowledgeI got so passionate about technology. Hacking to me was like a video game. It was about getting trophies. I just kept going on and on, despite all the trouble I was getting into, because I was hooked.
Tags: Game, Getting, TechnologyIt was used for decades to describe talented computer enthusiasts, people whose skill at using computers to solve technical problems and puzzles was - and is - respected and admired by others possessing similar technical skills.
Tags: Computers, Others, ProblemsIt's actually a smarter crime because imagine if you rob a bank, or you're dealing drugs. If you get caught you're going to spend a lot of time in custody. But with hacking, it's much easier to commit the crime and the risk of punishment is slim to none.
Tags: Actually, Risk, TimeOracle, for example, has even hired people to dumpster dive for information about its competitor, Microsoft. It's not even illegal, because trash isn't covered by data secrecy laws.
Tags: Example, Laws, TrashThen again, my case was all about the misappropriation of source code because I wanted to become the best hacker in the world and I enjoyed beating the security mechanisms.
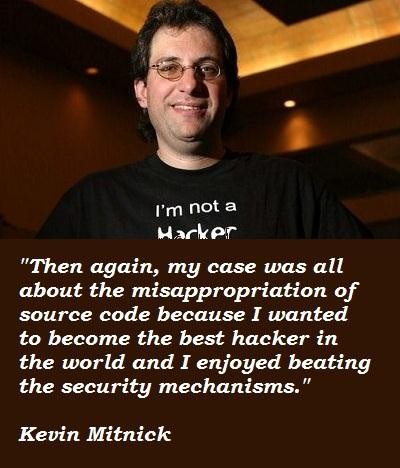
Tags: Become, Best, Wanted